A well-defined incident response plan helps you in following ways:
Effectively identify any cyber-attack.
Minimize the organization damages.
Protect your sensitive information.
Protect your reputation and customer trust.
Finding and fixing the cause to prevent future attacks.
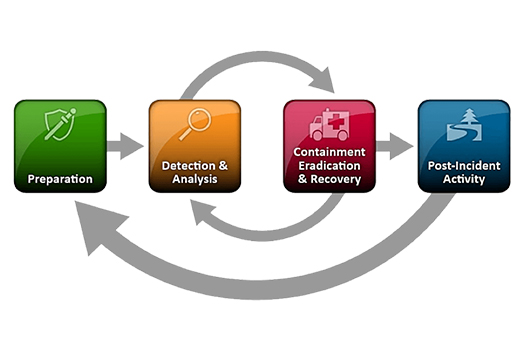
An Incident Response is carried out in various phases to ensure clear planning and delivery model.
Preparation: Our incident response team is ready to handle an incident at a moment’s notice which includes define a corporate security policy with proper strategy, communication and documentation.
Identification: Identify the incident that just happened. Initial identification of the incident will help us mitigate the incident asap.
Containment: In this stage we immediately response in order to stop spreading the threat and doing further damage. Back-up on all affected systems to save their current states for later forensics.
Eradication: We restore all the affected systems by disk cloning and update the defence system to prevent the same kind of security incident from occurring again.
Recovery: In this stage we bring all systems back into full production after verifying that they are clean and free.
Report: After gathering all the data, we analyse the data and provide you with a complete easy to understand report containing criticality level, risk, technical and business impact. In addition, we provide a detailed remediation strategy to avoid further incidents.
Presentation: The final phase in incident response will be a presentation of all documentation to you. We will walk you through the information provided, make any updates needed, and address questions regarding the incident.